

Journal of Contemporary Politics
Year: 2026, Volume: 5, Issue: 1, Pages: 14-22
Original Article
S S Adwaith1, Ashika S Prasad1*
1Research Scholar, Department of Political Science, University of Kerala, Kerala, India
*Corresponding Author
Email: [email protected]
Received Date:26 November 2025, Accepted Date:06 January 2026, Published Date:31 March 2026
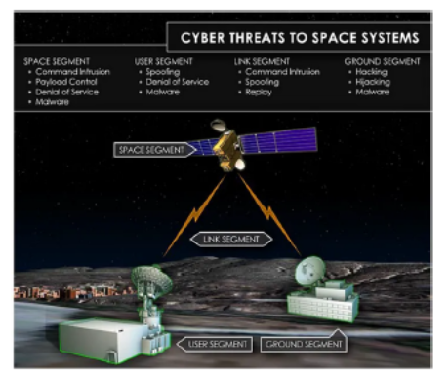
The intensity, frequency and scale of cyber-attacks define the warfare of the 21st century, and this has triggered a series of economic, political and social adjustments from the local to the international arena. Cyber-attacks are an emerging threat to space security. With the growing reliance on automation, there is a high risk of external agencies interfering with the operation of the satellite, cutting off the communication system and trying to obtain confidential data from the satellite. This paper seeks to identify cyber threats to space assets and analyse their implications for India’s security, applying a realist perspective and focusing on China’s rise as a space-cyber power.
Keywords: Space Assets, Cyber Security, Space Security, India, China
1. Ear E, Remy JLC, Feffer A, Xu S. Characterizing Cyber Attacks against Space Systems with Missing Data: Framework and Case Study. 2023 IEEE Conference on Communications and Network Security (CNS). 2023; Available from: https://doi.org/10.1109/cns59707.2023.10289045
2. Wess M. (2021, February 1). <I>ASAT Goes Cyber</I>. U.S. Naval Institute. https://www.usni.org/magazines/proceedings/2021/february/asat-goes-cyber
3. Pearson J. (2022). Russia downed satellite internet in Ukraine -Western officials. <I>Reuters</I>. https://www.reuters.com/world/europe/russia-behind-cyberattack-against-satellite-internet-modems-ukraine-eu-2022-05-10/
4. Bhattacharya S. (2016). Explaining the Conceptualisation of Security in Mainstream International Relations Theory. <I>The Indian Journal of Political Science</I>, 77(1), 77–84. https://www.jstor.org/stable/26575669
5. Attinà F. Traditional Security Issues. China, the European Union, and the International Politics of Global Governance. 2016; Available from: https://doi.org/10.1057/9781137514004_10
6. Srikanth D. (2014). Non-Traditional Security Threats In The 21st Century: A Review. <I>International Journal of Development and Conflict</I>, 4, 60–68.
7. Kremer JF, Müller B. Cyberspace and International Relations: Theory, Prospects and Challenges. 2014; Available from: https://doi.org/10.1007/978-3-642-37481-4
8. Rajagopalan RP. (2019). <I>Electronic and Cyber Warfare in Outer Space</I>. https://unidir.org/publication/electronic-and-cyber-warfare-in-outer-space/
9. CCSDS. (2022). <I>Security Threats Against Space Missions</I>. https://ccsds.org/Pubs/350x1g3.pdf
10. Baldwin DA. The concept of security. Review of International Studies. 1997; 23 (1). Available from: https://doi.org/10.1017/s0260210597000053
11. Waltz KN. (1997). <I>Theory of international politics (Reiss)</I>. Waveland Press
12. Khan SK, Shiwakoti N, Diro A, Molla A, Gondal I, Warren M. Space cybersecurity challenges, mitigation techniques, anticipated readiness, and future directions. International Journal of Critical Infrastructure Protection. 2024; 47 Available from: https://doi.org/10.1016/j.ijcip.2024.100724
13. Shabbir Z, Sarosh A. Counterspace Operations and Nascent Space Powers. Astropolitics. 2018; 16 (2). Available from: https://doi.org/10.1080/14777622.2018.1486792
14. Partlow RG. (2010). <I>Space System Vulnerabilities and Defenses [Air Command and Staff College, Air University]</I>. https://apps.dtic.mil/sti/pdfs/AD1019732.pdf
15. Yates H, Grimaila MR. (2008). <I>A Systematic Approach for Securing our Space Assets. Faculty Publications</I>. https://scholar.afit.edu/facpub/160
16. Khan A. (2020, August 1). <I>Cyber ASAT-Capabilities and South Asia. Modern Diplomacy</I>. https://moderndiplomacy.eu/2020/08/01/cyber-asat-capabilities-and-south-asia/
17. Bailey B, Speelman RJ, Doshi PA, Cohen NC, Wheeler WA. (2019). Defending Spacecraft in the Cyber Domain. <I>The Centre for Space Policy and Strategy, The Aerospace Corporation</I>. https://aerospace.org/sites/default/files/201911/Bailey_DefendingSpacecraft_11052019.pdf
18. Nichols PRK, Carter CM, Ii JVD, Farcot M, Hood CJP, Jackson DMJ, <I>et al</I>. (2023). <I>Cyber-Human Systems, Space Technologies, and Threats</I>. New Prairie Press.
19. Varadharajan V, Suri N. Security challenges when space merges with cyberspace. Space Policy. 2024; 67 Available from: https://doi.org/10.1016/j.spacepol.2023.101600
20. Li D. Cyber-attacks on Space Activities: Revisiting the Responsibility Regime of Article VI of the Outer Space Treaty. Space Policy. 2023; 63 Available from: https://doi.org/10.1016/j.spacepol.2022.101522
21. Robinson J. (2016). The Space Review: Governance challenges at the intersection of space and cyber security. The Space Review. https://www.thespacereview.com/article/2923/1
22. Martin AS. Outer Space, the Final Frontier of Cyberspace: Regulating Cybersecurity Issues in Two Interwoven Domains. Astropolitics. 2023; 21 (1). Available from: https://doi.org/10.1080/14777622.2023.2195101
23. King M, Goguichvili S. (2020). <I>Cybersecurity Threats in Space: A Roadmap for Future Policy</I>. Wilson Centre. https://www.wilsoncenter.org/blog-post/cybersecurity-threats-space-roadmap-future-policy
24. Livingstone D, Lewis P. (2016). <I>Space, the Final Frontier for Cybersecurity?</I> The Royal Institute of International Affairs, Chatham House. https://www.chathamhouse.org/sites/default/files/publications/research/2016-09-22-space-final-frontier-cybersecurity-livingstone-lewis.pdf
25. Jinghua L. (2019, March 22). <I>What Are China’s Cyber Capabilities and Intentions?</I> International Peace Institute. https://theglobalobservatory.org/2019/03/what-are-chinas-cyber-capabilities-intentions/
26. The International Institute for Strategic Studies. (2022). <I>China’s Cyber Influencing and Interference</I>. https://www.iiss.org/globalassets/media-library---content--migration/files/research-papers/2022/02/great-power-offensive-cyber-campaigns_04-china.pdf
27. Finkelstein DM. (2021). <I>The PLA’s New Joint Doctrine: The Capstone of the New Era Operations Regulations System</I>. CNA. https://www.cna.org/reports/2021/09/The-PLAs-New-Joint-Doctrine.pdf
28. Yuan Y. (2023, January 29). Chinese Thinking on the Space-Cyber Nexus. <I>Centre for International Governance Innovation</I>.
29. Yu J. (2020). <I>Satellite Internet, bringing the ‘Base Station’ to Space (New Technology, New Progress)</I>. People.Cn. http://scitech.people.com.cn/n1/2020/0810/c1007-31815964.html.
30. Chopra A. (2021). People’s Liberation Army Stratgic Support Force: Implications and Options for India. <I>Air Power</I>, 16(3). https://capsindia.org/wp-content/uploads/2022/01/Anil-Chopra.pdf
31. Pollpeter K, Chase M, Heginbotham E. (2017). <I>The creation of the PLA Strategic Support Force and its implications for Chinese military space operations</I>. RAND Corporation.
32. Levite A, Jinghua L, Perkovich G, Chuanying L, Manshu X, Bin L, <I>et al</I>. (2021). <I>China-U.S. Cyber-Nuclear C3 Stability. Carnegie Endowment for International Peace</I>. https://carnegieendowment.org/files/Levite_et_all_C3_Stability.pdf
33. Odgaard L. NATO’s China Role: Defending Cyber and Outer Space. The Washington Quarterly. 2022; 45 (1). Available from: https://doi.org/10.1080/0163660x.2022.2059145
34. Kashiwagi R. (2021). <I>Japan aerospace cyberattacks show link to Chinese military: Police</I>. Nikkei Asia. https://asia.nikkei.com/Business/Technology/Japan-aerospace-cyberattacks-show-link-to-Chinese-military-police
35. Lee Y. (2022). Cyberspace governance in China: Evolution, features and future trends. <I>Institut Français des Relations Internationales (Ifri)</I>. https://www.ifri.org/sites/default/files/migrated_files/documents/atoms/files/lee_cyberspace_governance_china_2022.pdf
36. U.S.-China Economic and Security Review Commission. (2025). <I>Artificial eyes: Generative AI in China’s military intelligence (Insikt Group Report)</I>. Recorded Future. https://assets.recordedfuture.com/insikt-report-pdfs/2025/ta-cn-2025-0617.pdf
37. The PLA goes back to school: Mapping new developments in China’s military cyber education system. (2025, September 25). <I>Margin Research</I>. https://margin.re/2025/09/the-pla-goes-back-to-school-mapping-new-developments-in-chinas-military-cyber-education-system/
38. Simon T. (2023, January 29). Cyberproofing India’s Space Assets. <I>Centre for International Governance Innovation</I>. https://www.cigionline.org/articles/cyberproofing-indias-space-assets/
39. Gill P. (2021, April 9). The Chinese cyber threat is real, and India’s best defence right now is to keep its outage time limited. <I>Business Insider</I>. https://www.businessinsider.in/defense/news/the-chinese-cyber-threat-is-real-and-indias-best-defence-right-now-is-to-keep-its-outage-time-limited/articleshow/81981886.cms
40. The Defense Post. (2022, April 8). <I>India Claims It Foiled Chinese Cyber-Attack on Disputed Border</I>. https://www.thedefensepost.com/2022/04/08/india-chinese-cyber-attack/
41. Uppal R. (2023, February 14). <I>With Rising threat in Space domain from Electronic to Cyber Warfare, Space agencies enhancing Cyber security measures</I>. IDST, English.
© 2026 Published by Bangalore University. This is an open-access article under the CC BY license (https://creativecommons.org/licenses/by/4.0/)
Subscribe now for latest articles and news.